Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
The account data review for identifiers 8285431493, mez68436136, 9173980781, 7804091305, and IP 111.90.150.204l initiates a structured evaluation of provenance, access patterns, and privilege boundaries. The approach emphasizes credential tracing, activity signals, and data integrity checks to identify gaps. Findings must be validated against governance standards before remediation actions are considered. The outcome hinges on precise documentation and reproducible methods, inviting further examination of each element to determine next steps.
What Is Account Data Review and Why It Matters
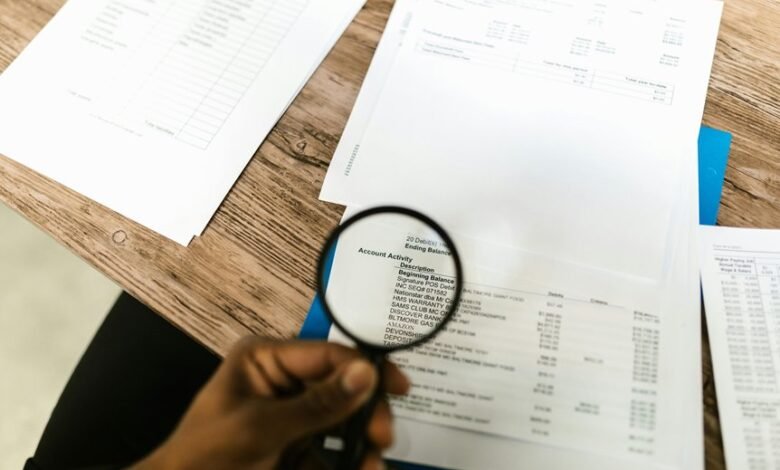
Account data review is a structured process for evaluating the accuracy, completeness, and consistency of data stored in an organization’s systems.
The practice clarifies data provenance, enhances decision making, and strengthens governance.
Its significance lies in sustaining trust, enabling compliant reporting, and supporting risk management.
The review importance rests on transparency, reproducibility, and measurable improvements in data quality and operational efficiency.
Auditing Credentials and Identifiers: A Practical Checklist
Auditing credentials and identifiers is a logical extension of ensuring data accuracy and governance established in the prior review. The checklist methodically verifies identity sources, credential lifecycles, and privilege boundaries, emphasizing accountability and reproducibility. It aligns with accounting controls and data provenance, enabling traceable changes, minimized risk, and auditable records. Clear criteria support disciplined evaluation without sensationalism or ambiguity.
Monitoring Data Access and Activity: Tools and Signals
Monitoring data access and activity entails a systematic assessment of how data is queried, retrieved, and modified across systems.
The discussion evaluates tools and signals that reveal usage patterns, anomalies, and throughput, aligning with privacy controls and governance requirements.
It emphasizes access patterns, baseline behaviors, and alerting mechanisms, enabling timely detection while preserving user autonomy and operational efficiency.
Validating Findings and Closing Gaps: Remediation and Governance
Data validation follows from the assessment of access and activity, establishing a frame to confirm or refute identified gaps. Remediation translates findings into actionable steps, prioritized by risk, feasibility, and impact. Governance formalizes accountability, oversight, and traceability, ensuring repeatable outcomes.
Account governance and data stewardship align roles with controls, sustaining disciplined improvements while enabling freedom through transparent, verifiable remediation and continuous monitoring.
Frequently Asked Questions
How Often Should Account Data Reviews Be Conducted?
Account data reviews should be conducted regularly, typically quarterly or semi-annually, depending on risk. The process evaluates data retention, access controls, and policy adherence, ensuring continuous improvement and safeguarding freedom through disciplined, transparent governance.
Which Roles Should Approve Remediation Actions?
Remediation actions should be approved by data owners, governance leads, and security officers, ensuring accountability. This aligns with data ownership and remediation workflows, providing analytical oversight while preserving freedom through clear, auditable decision-making processes.
What Are Correlated Indicators of Data Exfiltration?
Correlated indicators of data exfiltration include unusual outbound traffic and anomalous file transfers; risk indicators emphasize rapid data movement and credential abuse. Network monitoring techniques detect patterns, anomalies, and unexpected destinations to methodically assess potential data exfiltration risk indicators.
How Is Data Classification Defined for Review Scope?
Data classification for review scope is defined by data governance policies and risk assessment criteria, identifying sensitivity, owner, and access controls; analysts categorize data accordingly, establishing boundaries and sampling requirements to ensure comprehensive, compliant evaluations.
What Metrics Measure Review Effectiveness Over Time?
Metrics measure review effectiveness over time via trend analyses, sampling accuracy, and remediation rates, reflecting consistent data integrity and access governance performance. The approach is systematic, repetitive, and rigorous, ensuring trustworthy governance without infringing on freedom, exploratory data use.
Conclusion
This review treats the identifiers and IP as guardrails for provenance and access controls, testing whether credential origins align with observed activity. The theory that gaps in privilege boundaries predict exposure is challenged by mixed signals: some accounts show consistent patterns, others reveal anomalous access. Methodically, synchronization of provenance data with access signals narrows risk horizons. Conclusion: only through convergent evidence—traceable sources, guardrails, and remediation timelines—can governance achieve reproducible, transparent risk reduction and accountable stewardship.




