Nova Prism Start 402-378-9668 Unlocking Caller Data Systems

Nova Prism Start 402-378-9668 Unlocking Caller Data Systems presents a framework for secure, auditable access to disparate caller data sources. The approach emphasizes privacy-preserving architectures, standardized identifiers, and strict access controls, with clear governance and traceable processing pipelines. While it outlines modular components and real-world workflows, questions remain about implementation specifics, risk management, and regulatory alignment as teams consider adoption. This tension invites careful consideration and further examination of practical safeguards and efficacy.
What Is “Unlocking Caller Data Systems” and Why It Matters
Unlocking Caller Data Systems refers to the process of accessing and integrating information about telephone callers from various data sources. The practice centers on responsible data handling, transparency, and accountability. It clarifies how identifiers, metadata, and behavior profiles are assembled.
Emphasis rests on unlocking data while maintaining privacy, ensuring access governance, minimizing risk, and preserving user autonomy within compliant, auditable frameworks for informed regions and audiences seeking freedom.
Core Technologies Powering Caller Data Access
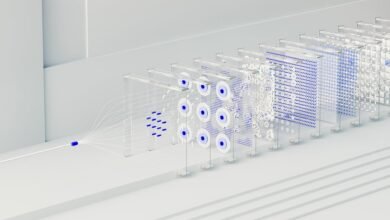
Core technologies powering caller data access encompass a framework of secure data collection, standardized identifiers, and auditable processing pipelines. The approach emphasizes interoperability, robust access controls, and traceable transformations. Unlocking architecture supports modular, privacy-preserving workflows, while data stewardship ensures governance and accountability. Cautious implementation reduces risk, enabling compliant data sharing and controlled analysis within transparent, auditable systems. Freedom-oriented design remains the aspirational baseline.
Real-World Use Cases and Workflows
Real-world use cases demonstrate how caller data access frameworks translate secure collection and auditable workflows into tangible benefits.
Implementations illustrate data governance in practice, balancing oversight with operational efficiency.
Organizations adopt structured access orchestration to minimize risk while preserving agility, aligning teams around consistent processes.
The workflow approach emphasizes traceability, repeatability, and compliance, enabling scalable, transparent decision-making without compromising freedom to innovate.
Privacy, Security, and Compliance Considerations for Teams
How should teams navigate privacy, security, and compliance when handling caller data across complex workflows? The assessment emphasizes privacy governance frameworks, risk-based controls, and regulatory alignment. Implement data minimization by restricting exposure to essential data only, deploy robust security controls, and enforce rigorous access auditing. Documentation, monitoring, and periodic audits prove accountability and sustain trust while preserving operational freedom and scalable collaboration.
Conclusion
The program’s impact on unlocking caller data is monumental, cascading through organizations with the precision of a laser and the reliability of a trained watchdog. By codifying auditable processes, standardized identifiers, and strict access controls, it promises near-omniscient visibility while maintaining airtight privacy boundaries. Yet, the system remains exquisitely cautious, resisting hype with rigorous governance, continuous monitoring, and careful risk assessment. In this tightly regulated arena, scale is matched by discipline, ensuring trustworthy, compliant data collaboration at every step.